This integration with Okta is currently under development and is not available to customers yet. Please contact us to learn more. |
If your organization uses Okta to manage your employees access to tools and services, you can take advantage of Okta’s “Provisioning” feature to automatically maintain traveller profiles in Umbrella Faces for your users.
The integration between Okta and Contentful that enables this provisioning to occur is built around an industry-standard protocol known as SCIM (System for Cross-domain Identity Management). To learn more about how Okta works with SCIM, please see this article.
The following provisioning features are currently supported by Umbrella Faces
| Feature | Description |
|---|---|
| Create users | Users in Okta that are assigned to the Umbrella Faces application are automatically added as travellers to Umbrella Faces. |
| Update user attributes | Updating an user in Okta will also update the linked attributes in Umbrella Faces |
| Deactivate users | Unassigning Users from Umbrella Faces in Okta will cause the associated traveller profile to be removed from Umbrella Faces. Please note: Faces does not recognize an "active" state on a profile. Hence if a profile is set to inactive it will be deleted along with all associated data |
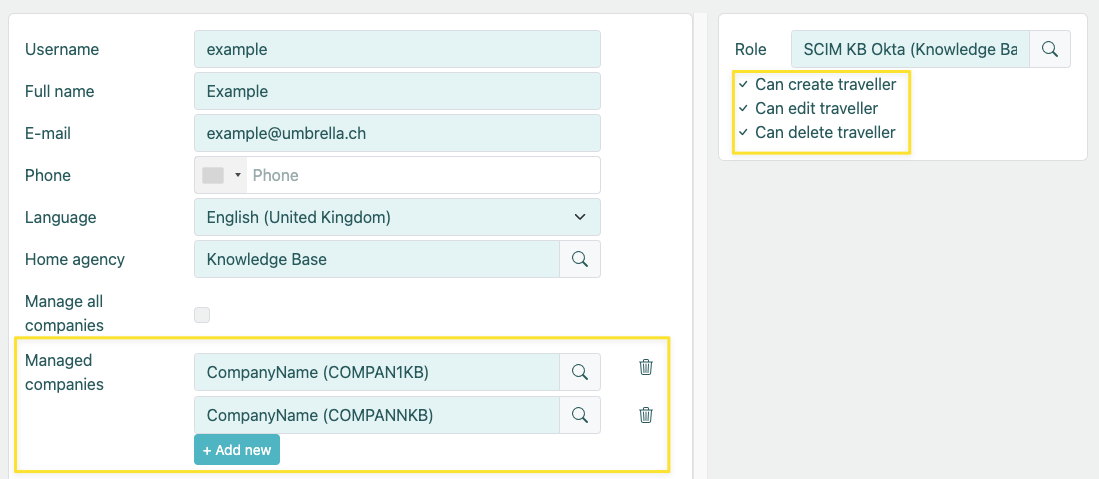
In order to use SCIM provisioning you will need to be an existing Faces customer and in possession of an administrative account which is allowed to manage traveler profiles. The administrative account can either be a Company- or Agency-Administrator
Please note that SCIM can be enabled in a self-service fashion, but will incur an additional charge once activated.
While it is possible to use any administrator, we do recommend creating a dedicated user account with access limited to the scope of the integration. (e.g. Company Administrator account with "Can Crate / Edit / Delete Traveller" rights)
Log in to your Okta admin portal and complete the following steps:
Click on the "Sign On" tab in the application.
Under "Credentials Details" select "Email" for the "Application username format"
Under the "Advanced Sign-On Settings" section enter the Faces Base URL in the field.
This should be the address of where you login to Faces minus the "/login" portion. For example if you usually login at https://tenzing.umbrella.ch/faces/login you'll have to enter https://tenzing.umbrella.ch/faces

Under the “Settings” panel on the left side, click “To App” under the Settings panel on the left.
Click the "Edit" button at the top right. Check the “Enable” box next to “Create Users”, "Update User Attributes" and "Deactivate Users"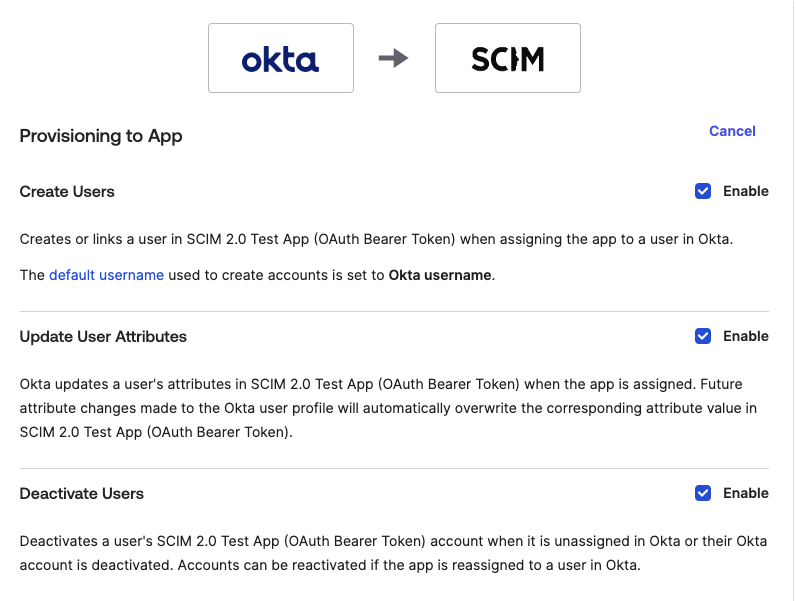
You should now be able to assign your Okta users to the Umbrella Faces application as needed, with their profiles automatically showing up as traveller profiles.
To configure additional field mappings between Okta and Umbrella Faces perform the following steps:
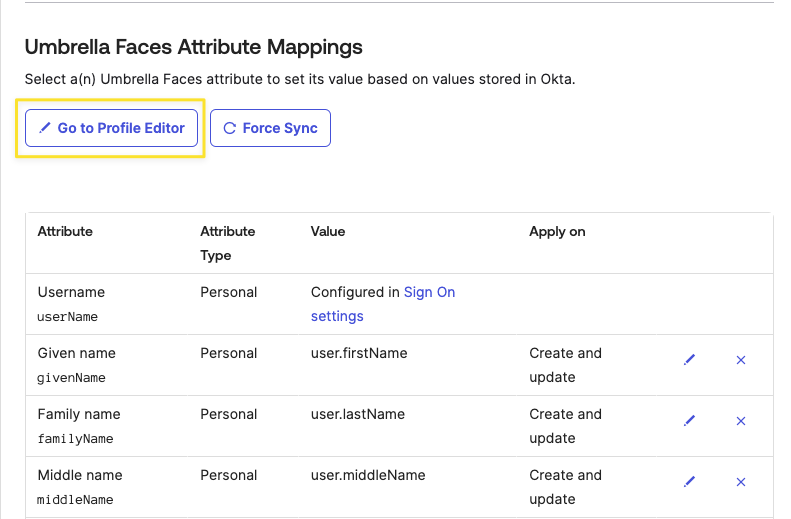
Within the profile editor you'll be able to change the predefined mappings as well as add additional mappings for custom data fields within Faces.
| Known Issue / Limitation | Solution |
|---|---|
| Faces does not support deactivation of travellers | Whenever a profile is set to inactive, we will delete it on our end. |
| Supported Data fields | The following standard SCIM fields are supported:
Additionally, we support custom attributes as defined in "Attribute Definitions" below. Please do not hesitate to reach out to us should you wish for further data fields to be made available |
By default this attribute is mapped to 'EXAMPLE', you'll want to update this to reflect an actual company shortname, either statically or via a function or other data field. |
At the very least, Umbrella Faces will require you to setup a mapping for "company_shortname", which is responsible for mapping the travellers to the correct company within Faces.
| External name | company_shortname |
|---|---|
| External namespace | urn:ietf:params:scim:schemas:extension:umbrellafaces:2.0:Traveller |
| Example |
|
To setup a mapping of a generic field value, first find the field name from the Umbrella Faces administrative UI
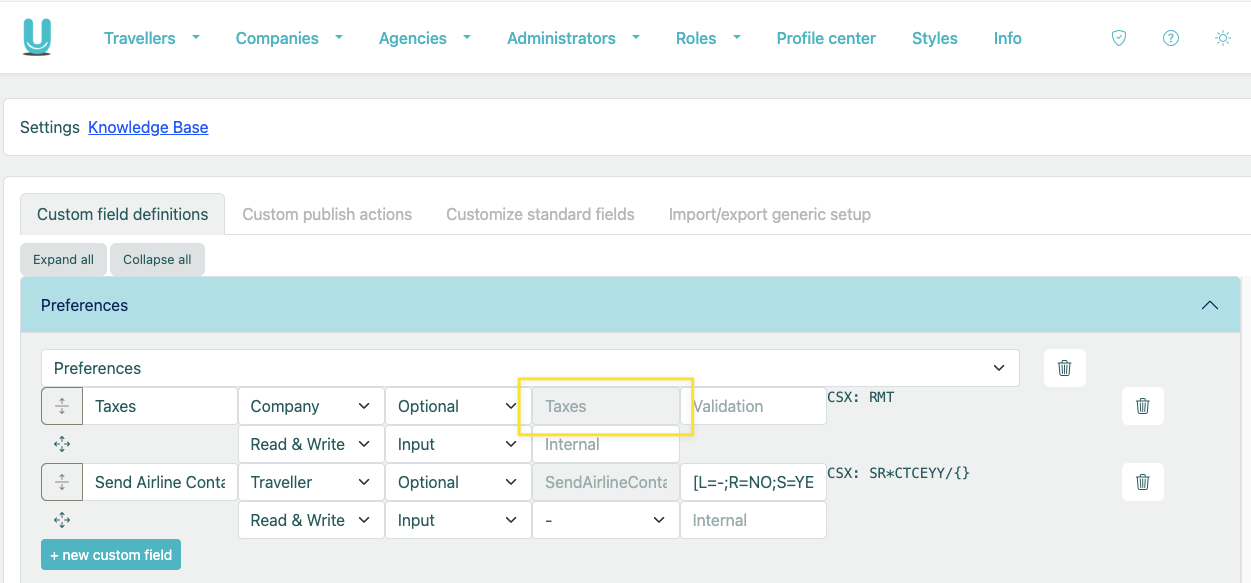
Then setup the attribute in Okta as follows and add a mapping
| External name | generic_fields.^[type=='UmbrellaFacesFieldName'].value |
|---|---|
| External namespace | urn:ietf:params:scim:schemas:extension:umbrellafaces:2.0:Traveller |
| Example |
|